Alternative Energy
Ensuring Compliance and Security in Government IT Services

In an era where cyber threats are evolving by the day, ensuring compliance and security in government IT services is more crucial than ever. Governments hold vast amounts of sensitive data, making them prime targets for cyberattacks. The guide below provides valuable guidance on how to protect this information while maintaining regulatory compliance. Read on to discover actionable tips that can help you secure your government IT services effectively.
Implement Comprehensive Security Policies
One of the first steps to ensuring compliance and security is establishing robust security policies. These policies should cover everything from data encryption to access controls, and they should be regularly reviewed and updated to adapt to new threats.
Example:
The U.S. Department of Defense (DoD) regularly updates its Cybersecurity Maturity Model Certification (CMMC) to provide a standardized set of security controls.
Tip:
Ensure your security policies include guidelines for incident response, regular audits, and employee training.
Conduct Regular Security Audits
Regular security audits are essential for identifying vulnerabilities before they can be exploited. These audits can help you understand the effectiveness of your current security measures and highlight areas for improvement.
Example:
The UK Government’s National Cyber Security Centre (NCSC) recommends conducting at least two comprehensive security audits annually.
Tip:
Use both internal and external auditors to get a balanced view of your security posture.
Train Employees on Cybersecurity Best Practices
Human error is often a significant factor in security breaches. Regular training can educate employees about cybersecurity best practices, making them an integral part of your security framework.
Example:
The Australian Cyber Security Centre (ACSC) offers a range of training programs to help government employees stay up-to-date with the latest cybersecurity threats and protective measures.
Tip:
Incorporate phishing simulations and interactive modules into your training programs to keep employees engaged.
Utilize Multi-Factor Authentication (MFA)
Multi-Factor Authentication adds an extra layer of security by requiring multiple forms of identification before granting access to sensitive information. This reduces the risk of unauthorized access significantly.
Example:
The General Services Administration (GSA) mandates the use of MFA for all its employees and contractors.
Tip:
Consider using biometrics or hardware tokens as part of your MFA strategy for added security.
Encrypt Sensitive Data
Data encryption ensures that even if data is intercepted, it cannot be read without the appropriate decryption key. This is particularly important for sensitive government information.
Example:
The European Union’s General Data Protection Regulation (GDPR) strongly advocates for the encryption of personal data to protect it from unauthorized access.
Tip:
Use end-to-end encryption for data in transit and at rest to ensure comprehensive protection.
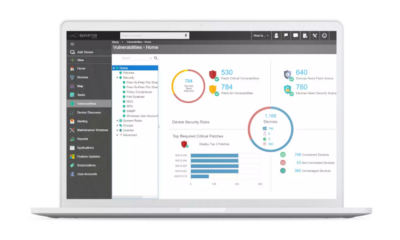
Monitor Network Activity
Continuous monitoring of network activity can help identify suspicious behavior in real-time, allowing for quicker responses to potential threats.
Example:
The Cybersecurity and Infrastructure Security Agency (CISA) provides guidelines for continuous diagnostics and mitigation programs to help monitor and respond to security incidents.
Tip:
Implement automated monitoring tools that use AI and machine learning to detect anomalies.
Ensure Compliance with Regulatory Standards
Government IT services must comply with various regulatory standards to ensure data protection and privacy. Familiarize yourself with relevant regulations and ensure your security measures align with them.
Example:
The Health Insurance Portability and Accountability Act (HIPAA) outlines specific requirements for protecting health information in the United States.
Tip:
Conduct regular reviews to ensure continued compliance with evolving regulations.
Foster a Culture of Security
Creating a culture that prioritizes security can make a significant difference in how effectively your organization can protect its data. Encourage open communication about security issues and reward proactive behavior.
Example:
The Canadian Centre for Cyber Security encourages a culture of security through its public awareness campaigns and organizational initiatives.
Tip:
Host regular security awareness workshops and encourage employees to report potential security issues without fear of reprisal.
Collaborate with Other Agencies
Collaboration with other government agencies and industry partners can provide valuable insights and resources for improving your security posture. Sharing information about threats and best practices can help create a more secure environment for everyone.
Example:
The Five Eyes Alliance, comprising intelligence agencies from the US, UK, Canada, Australia, and New Zealand, collaborates on cybersecurity efforts to enhance collective security.
Tip:
Join local and international cybersecurity forums and participate in joint exercises to stay ahead of emerging threats.
By implementing these strategies, government IT services can significantly enhance their security and ensure compliance with regulatory standards. Secure your systems today and safeguard the sensitive information entrusted to your care.